In today’s digital age, cybersecurity is paramount. Cyber-attacks can cause significant damage to a company’s reputation and bottom line. Understanding the nature of these threats and knowing how to respond is crucial. This article outlines essential steps to recover from a cyber-attack and provides a case study to help organizations enhance their security practices.
Understanding Cybersecurity and Cyber Attacks
Cybersecurity involves protecting internet-connected systems, including hardware, software, and data, from cyber-attacks. These attacks can come in various forms, each with different methods and consequences.
Common Types of Cyber Attacks
- Phishing: Attackers trick individuals into providing sensitive information through deceptive emails or websites.
- Malware: Malicious software designed to damage, disrupt, or gain unauthorized access to systems.
- Ransomware: A type of malware that encrypts data and demands payment for the decryption key.
- DDoS (Distributed Denial of Service): Overloads a website with traffic, causing it to crash or become unavailable.
- SQL Injection: Attackers insert malicious SQL code into a query to manipulate the database and access sensitive data.
- Cross-Site Scripting (XSS): Attackers inject malicious scripts into webpages viewed by other users.
Common Types of Cyber Attacks
To safeguard against these attacks, organizations should implement robust security measures:
- Web Application Firewall (WAF): Filters and monitors HTTP traffic, blocking malicious traffic.
- Regular Updates: Keep all software, plugins, and themes updated to their latest versions.
- Security Plugins: Use security plugins to add an extra layer of protection.
- Two-Factor Authentication (2FA): Adds an extra step for logging in, making it harder for attackers to gain access.
- SSL Certificate: Encrypts data transmitted between the user’s browser and your server.
- Regular Backups: Ensure all critical data is regularly backed up and stored offline to mitigate data loss during an attack.
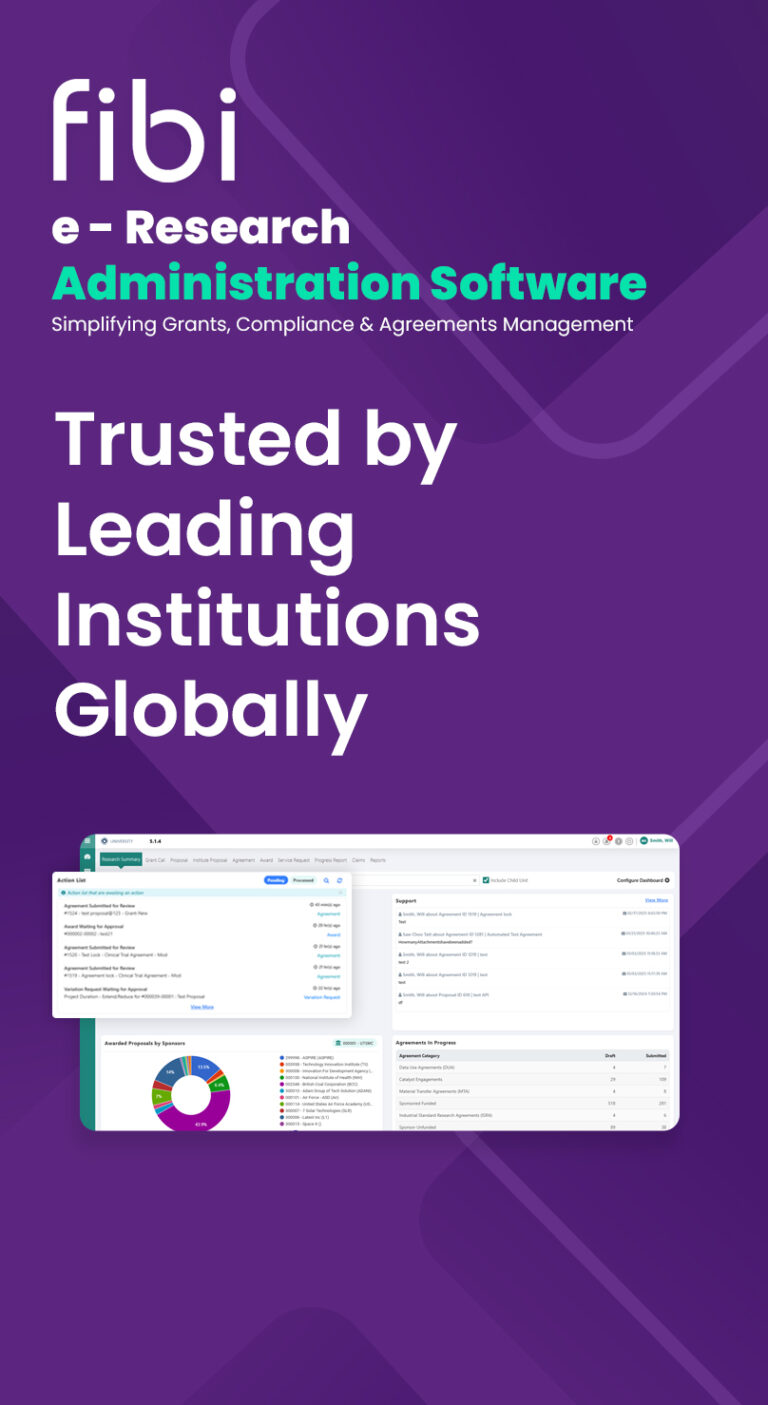
Case Study: Responding to a Cyber Attack
This case study illustrates the steps taken to recover and secure a website after an unexpected outage caused by a hack.
Scenario: A website with critical data was hacked through a DDoS (Distributed Denial of Service) attack. The attacker overloaded the website with traffic, causing it to crash and become unavailable. This was done by injecting malicious crone jobs to automate the execution of scripts that generated excessive traffic towards the target server. As a result, the allocated resources for managing the traffic were exhausted, and the website went down.
Immediate Steps to Recover from a Cyber Attack
- Take the Website Offline: The website was immediately taken offline to prevent attackers from causing additional harm.
- Inform the Hosting Provider: The hosting provider was promptly informed about the breach. They assisted by providing detailed logs, temporary access restrictions, and additional technical support.
- Change All Passwords: All passwords associated with the website, including admin accounts, databases, and FTP accounts, were immediately changed to prevent further unauthorized access.
- Check for Malware: A thorough scan was performed to identify and eliminate any malware that may have been installed during the attack.
- Identify the Type of Attack: The type of breach was identified to plan the appropriate response. Understanding the nature of the attack is crucial for effective remediation.
- Remove Malicious Code: Malicious code was removed to clean the website and restore its original state.
Implementing Security Measures
To prevent future attacks, the following security measures were implemented:
- Web Application Firewall (WAF)
- Regular Software Updates
- Security Plugins
- Two-Factor Authentication (2FA)
- SSL Certificate
- Regular Offline Backups
Conclusion
This incident underscored the importance of robust security practices and constant vigilance in maintaining website security. By taking immediate action and implementing comprehensive security measures, the website and its data was not only recovered but also fortified against future attacks. This case study serves as a guide for handling similar incidents and highlights the critical steps necessary for recovery and securing a compromised website.
Key Takeaways
- Proactive Prevention: Implement strong security measures to prevent attacks.
- Immediate Response: Act quickly to mitigate damage if an attack occurs.
- Ongoing Vigilance: Regularly update security practices and stay informed about new threats.
- Backup Data: Regularly back up critical data and store it offline for quick recovery in case of an attack.